Sometimes, it can seem like just when you think you’re safe, events occur to show you that you couldn’t have been closer to harm. Such is the case with the recent master key vulnerability uncovered in Android devices.
While technology has allowed us to be more secure on the web than ever, something it has also allowed for is the development of more sophisticated tools for hackers to use to try and overcome those security measures. Indeed, the battle between security measures and those who would break them is never-ending. And this is probably best illustrated by the discovery of the “Master Key”.
What is the Master Key?
The “Master Key” vulnerability was named as such due to its ability to be successful with any app installed on an Android device. The vulnerability would allow any attacker the ability to make modifications to any apps installed with the simple insertion of a malicious file having the same name as a file already in an application package. This could mean the installation of a Trojan, malware, or any other manner of information-gathering program.
Once opened, the Android device validates the digital signature of the first file, but not of the second because the file appears to have been validated previously. The ability of the Master Key vulnerability to basically render legitimate apps malicious was what caused a main concern among Android users and app developers alike: that the vulnerability could be used to create apps that looked legitimate, but that were malicious, with the ultimate goal of controlling devices completely. And that concern proved itself to be quite legitimate, as two of these apps have already been discovered in China, which has security experts fully expecting this type of app development to continue.
Lack of Patches Confirmed Last Year
Many may wonder why this vulnerability was even allowed to enter the wild, let alone why it had the ability to even be developed. Because according to at least one report last year, there were vulnerabilities that went un-patched in over half of the Android devices in use at the time.
This was discovered following scans with a vulnerability assessment tool for Android devices called X-Ray. The tool scanned Android devices for what are known as ‘privilege escalation vulnerabilities’, which can be exploited by malware.
Even in 2012, the slow deployment of Android security patches was mentioned as having been an issue for many years, the reasons for such slow movement being the manufacturer stopping the issuance of updates, and the inability of carriers to distribute those updates quickly enough.
Rising Mobile Device Usage Could Spell More Trouble
Interestingly, the slow release of patches to users is still considered to be a major reason for the proliferation of the master key vulnerability today. However, it’s suspected that the number of instances of exploited Android devices will continue to rise with the usage of these devices.
Thankfully, today there are several ways to scan and patch various applications. Some examples include ReKey, which alerts users to malicious application installation. Another is Bluebox, which has released an application for scanning for malicious apps on a device.
Expert Advice about Securing Devices from Apps Exploiting the Master Key Vulnerability
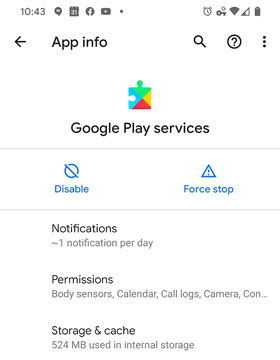
Whether this year or last, the advice has tended to be the same: getting your apps from an official marketplace may offer you the highest degree of security. Android users are urged to adhere to Google Play for application downloads, while avoiding those third-party sources often found in online communities, web sites and unofficial marketplaces.
Having a scanner application installed on your Android device can mean easy detection of applications attempting to exploit the master key vulnerability, as well as helping users to avoid installing suspicious apps that can result in the obtaining of personal information.